Venerdì 11 ottobre 2024 si terrà l'ottava edizione del Cybersecurity Day, un evento organizzato dall'Istituto di Informatica e Telematica del CNR nell'ambito del progetto SERICS. La giornata sarà dedicata alle più recenti attività di ricerca e innovazione nel...
NOTIZIE & EVENTI
BLOG & VIDEO
SERVIZI
|
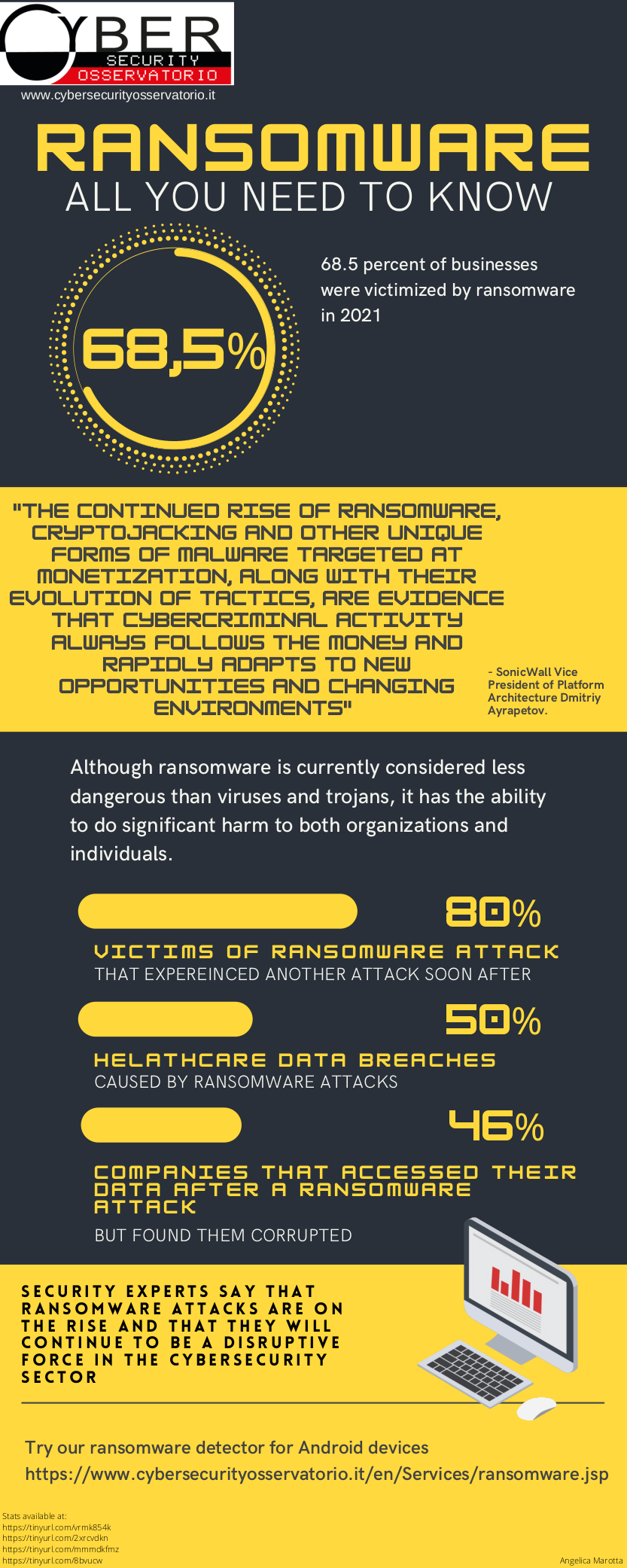
Il servizio si prefigge di individuare comportamenti tipici dei ransomware quali, ad esempio, la cifratura di una... |
Il servizio analizza un log di richieste DNS e identifica se all’interno sono stati risolti dei nomi a dominio che... |
Il Thesaurus offre una rappresentazione della conoscenza di un insieme di termini relativi alla Cybersecurity,... |
Servizio Rilevazione Malware. Il servizio permette di rilevare comportamenti malevoli in file (ad esempio, eseguibili o... |