Pubblicato il nuovo Rapporto Nazionale PID Cyber Check, un’analisi approfondita sul livello di sicurezza informatica delle imprese italiane, basata su un questionario di autovalutazione promosso dall’Osservatorio sulla Cybersecurity. Il sondaggio, disponibile online, ha coinvolto 2.928 imprese e...
NOTIZIE & EVENTI
BLOG & VIDEO
SERVIZI
|
Il servizio analizza gruppi di email file (formato .eml) per identificare le email indesiderate (SPAM). Il servizio... |
Il servizio raccoglie informazioni relative ad exploit pubblici aggiornati giornalmente attraverso il repository... |
Il Thesaurus offre una rappresentazione della conoscenza di un insieme di termini relativi alla Cybersecurity,... |
Il servizio offre una piattaforma che consente ai Registrar di verificare eventuali problemi di performance e sicurezza... |
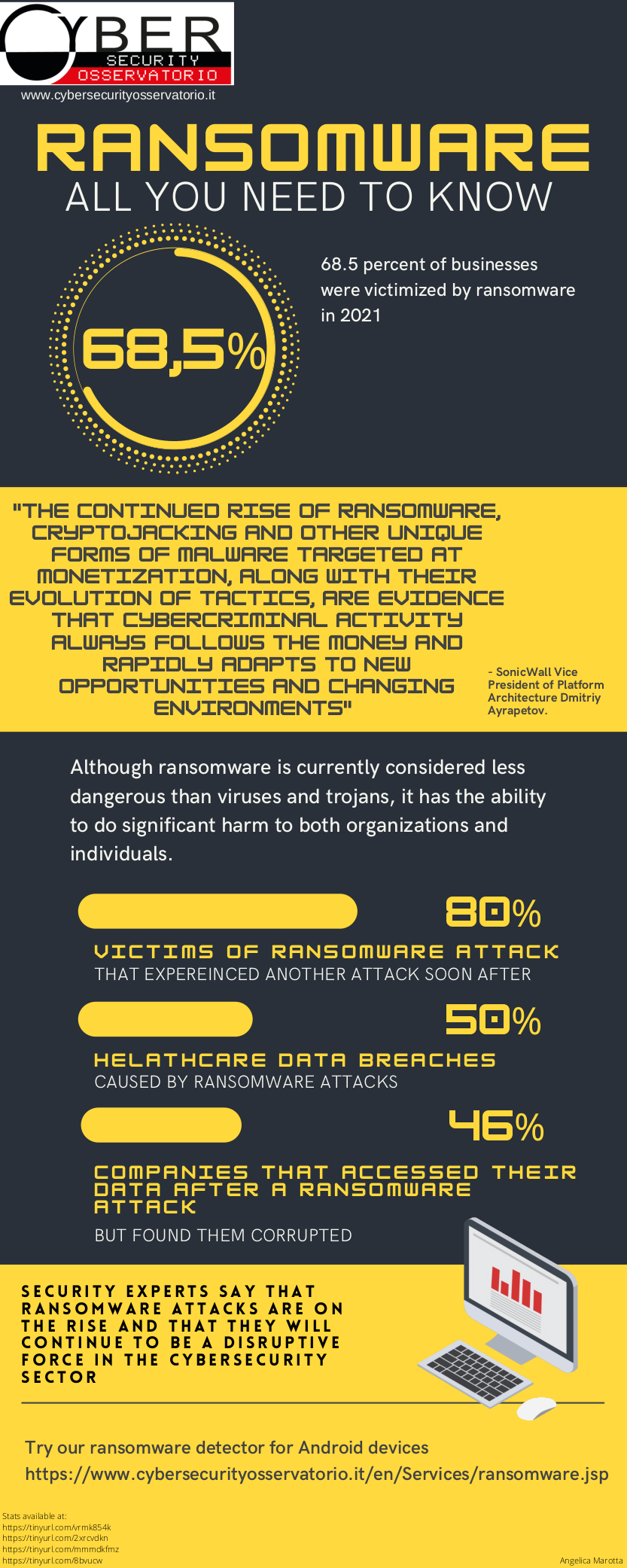
Infografica
CERT feeds
| Published | Title | URL |
|---|---|---|
| 11-09-2024 | Aggiornamenti per prodotti Zyxel (AL03/240911/CSIRT-ITA) | CERT LINK |
| 11-09-2024 | Aggiornamenti per prodotti Siemens (AL02/240911/CSIRT-ITA) | CERT LINK |
| 11-09-2024 | Aggiornamenti Mensili Microsoft (AL01/240911/CSIRT-ITA) | CERT LINK |
| 11-09-2024 | Aggiornamenti Mensili Microsoft (AL01/240911/CSIRT-ITA) | CERT LINK |
| 11-09-2024 | Vulnerabilità nei prodotti OwnCloud (AL09/240911/CSIRT-ITA) | CERT LINK |