Il 6 ottobre 2023 si terrà la settima edizione del Cybersecurity Day, un evento promosso dall'Istituto di Informatica e Telematica del CNR nell'ambito delle attività del progetto SERICS. Questa giornata intende offrire una serie di presentazioni incentrate su un...
NOTIZIE & EVENTI
BLOG & VIDEO
SERVIZI
|
Il servizio offre una piattaforma che consente ai Registrar di verificare eventuali problemi di performance e sicurezza... |
Il servizio offre un sondaggio per la verifica della conformità di un’organizzazione al GDPR (General Data Protection... |
Servizio Rilevazione Malware. Il servizio permette di rilevare comportamenti malevoli in file (ad esempio, eseguibili o... |
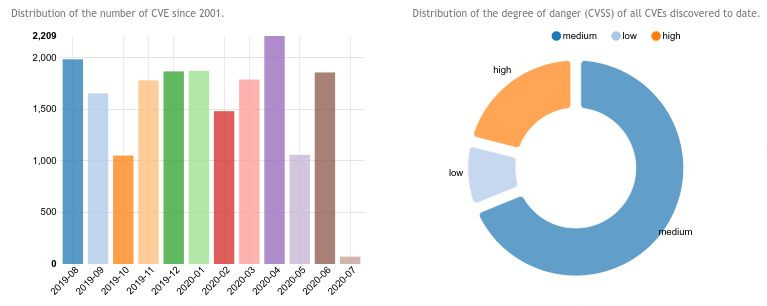
Il servizio raccoglie informazioni relative ad exploit pubblici aggiornati giornalmente attraverso il repository... |